Prioritize Vulnerabilities
That Actually Matter
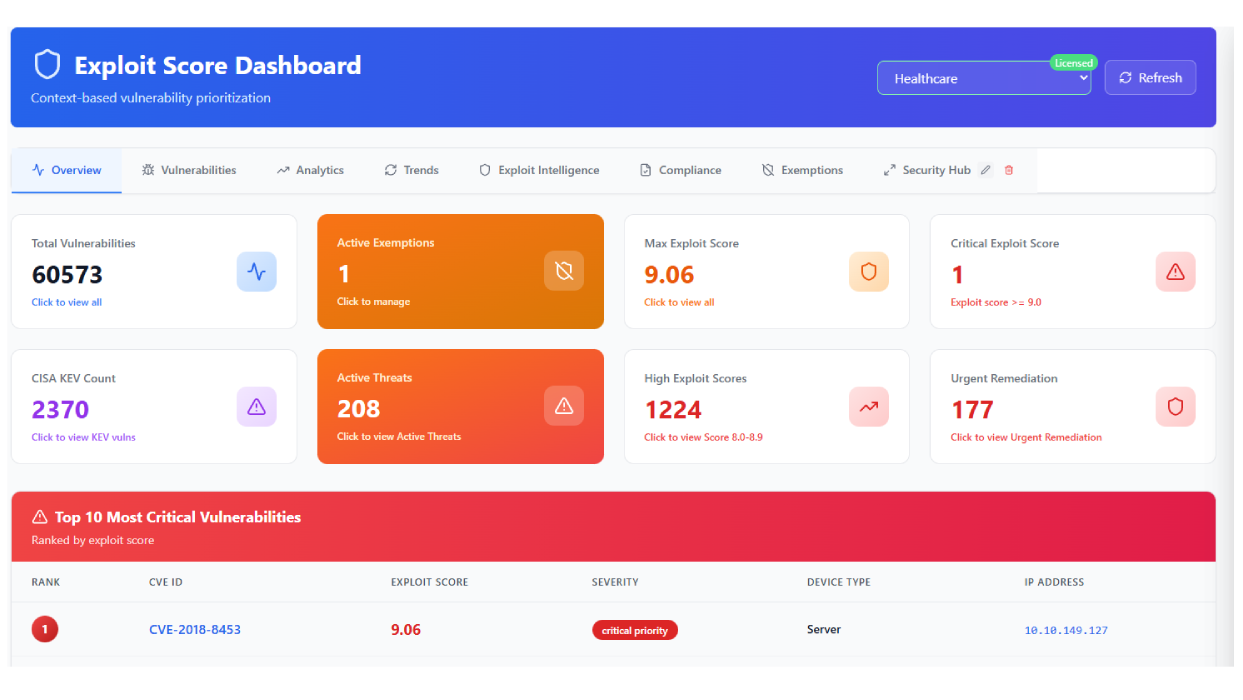
Stop chasing every CVE. Exploit Score uses machine learning to analyze real-world exploitability, helping your security team focus on threats that pose genuine risk to your organization.