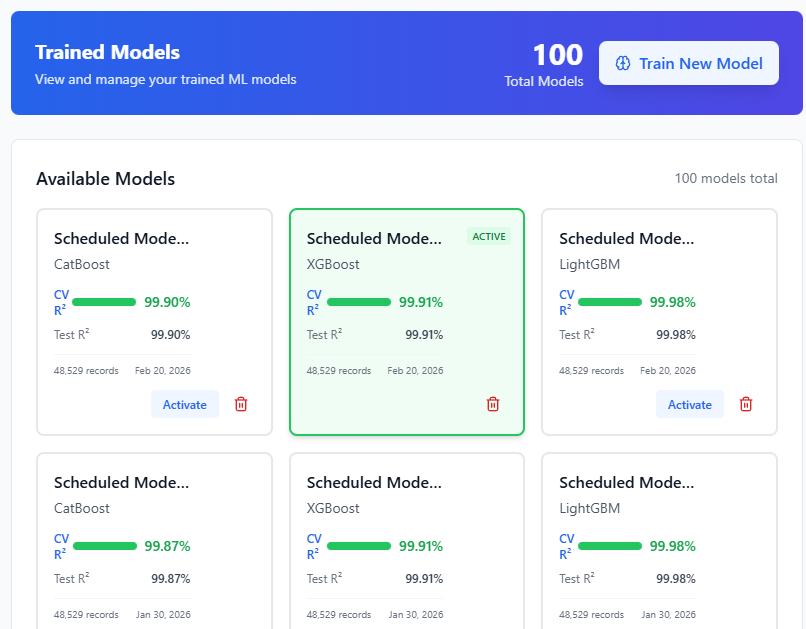
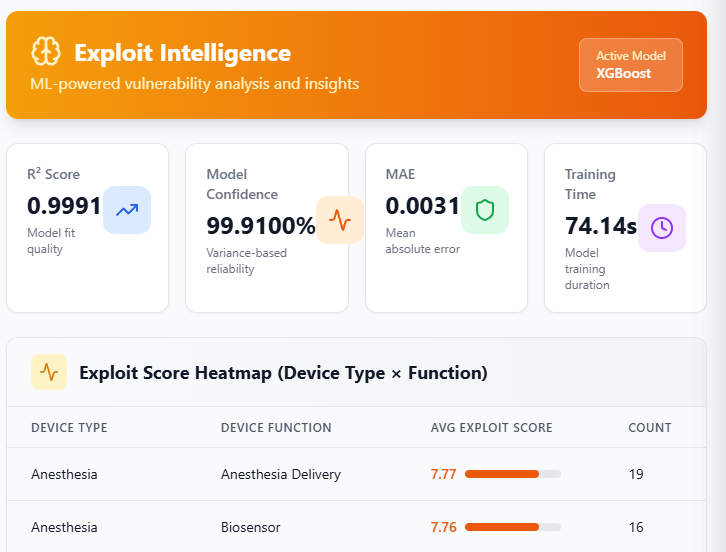
ML-Powered Exploit Scoring
Our machine learning models analyze multiple data sources to predict which vulnerabilities are most likely to be exploited in the real world.
- Trained on real-world exploit data
- K-fold cross-validation for accuracy
- Continuous model improvement
- Industry-specific model training
Threat Intelligence Integration
Stay ahead of threats with integrated intelligence from authoritative sources that inform your prioritization decisions.
- CISA Known Exploited Vulnerabilities (KEV)
- EPSS (Exploit Prediction Scoring System)
- NVD vulnerability database
- Real-time exploit monitoring
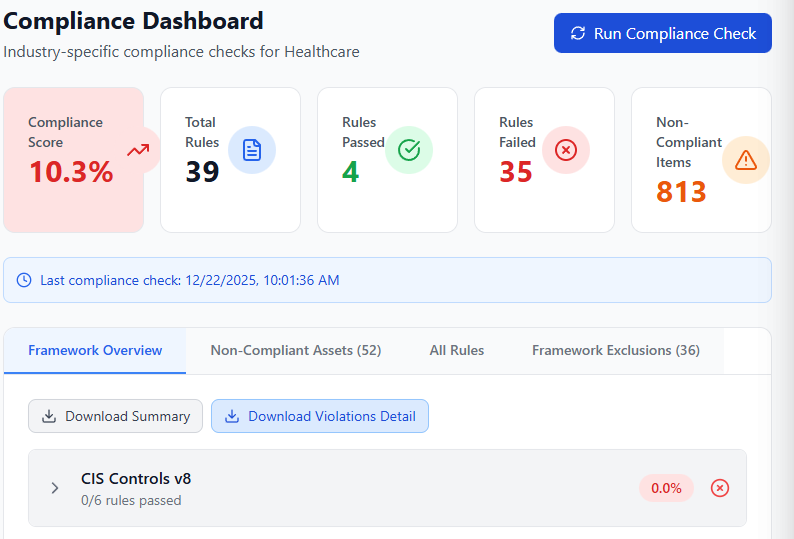
Compliance Framework Mapping
Map vulnerabilities directly to compliance requirements, making audits easier and ensuring regulatory alignment.
- PCI-DSS compliance tracking
- HIPAA security requirements
- SOC 2 control mapping
- Custom framework support