Vulnerability management has become one of the most resource-intensive responsibilities for security teams. With scan results routinely returning thousands of findings, the difference between an effective program and an overwhelmed one comes down to one thing: prioritization. Here are five practical steps to build a prioritization process that actually works.
Step 1: Establish Your Asset Inventory
You can't prioritize what you can't see. Before tackling vulnerability data, you need a clear picture of your environment:
- Identify all assets — Servers, workstations, network devices, cloud instances, containers, and applications. Shadow IT is the enemy of good prioritization.
- Classify by criticality — Not all systems are equal. A customer-facing payment server carries far more business risk than an internal dev sandbox. Assign criticality tiers (Critical, High, Medium, Low) based on the data it processes, the users it serves, and the impact if it were compromised.
- Map network exposure — Internet-facing assets are inherently at higher risk than those deep inside your network. Document which systems are externally accessible.
This asset context is the foundation of meaningful prioritization. Without it, every vulnerability is treated the same regardless of where it sits in your environment.
Step 2: Enrich Vulnerability Data with Threat Intelligence
Raw scanner output tells you what vulnerabilities exist. Threat intelligence tells you which ones matter right now. Layer these intelligence sources onto your vulnerability data:
- CISA KEV (Known Exploited Vulnerabilities) — If a CVE is on CISA's KEV list, it has been confirmed exploited in the wild. These should be treated as urgent regardless of their CVSS score.
- EPSS (Exploit Prediction Scoring System) — EPSS provides a probability score (0-1) estimating the likelihood that a vulnerability will be exploited in the next 30 days. A low-CVSS vulnerability with a high EPSS score deserves attention.
- Exploit availability — Is there public proof-of-concept code? Is it weaponized in exploit kits? The easier it is for an attacker to use, the higher the risk.
- Industry-specific threat feeds — Threat actors often target specific sectors. Healthcare organizations face different threats than financial institutions.
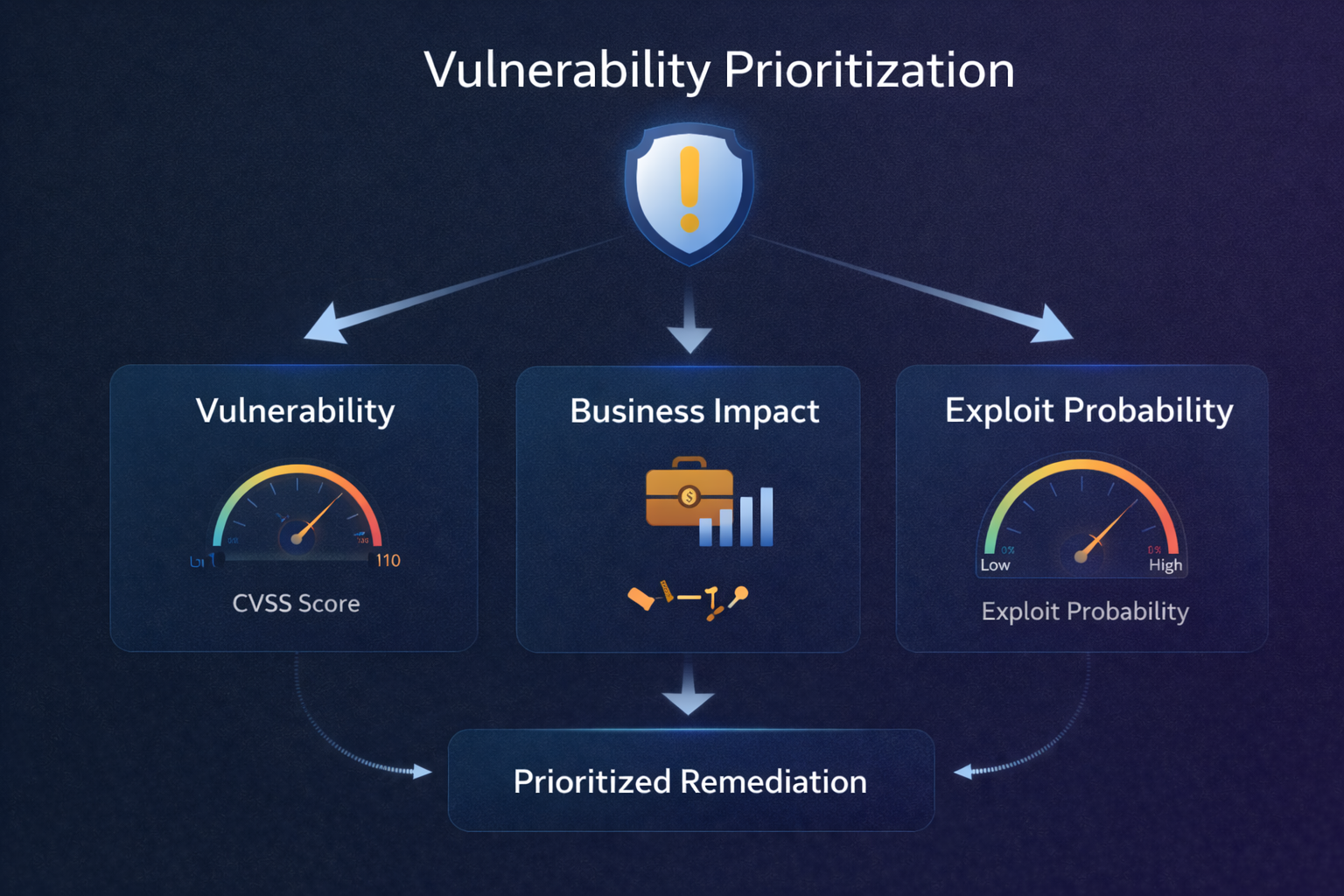
Step 3: Define Your Scoring Model
With asset context and threat intelligence in hand, you need a consistent method to combine these signals into a single priority score. An effective scoring model typically weighs:
- Technical severity (CVSS) as a baseline — but not the sole factor.
- Exploit likelihood (EPSS, KEV status, exploit availability) — heavily, because this is what separates theoretical risk from real-world danger.
- Asset criticality and exposure — a critical vulnerability on a critical asset is genuinely critical; the same vulnerability on a low-value, isolated system is not.
- Compensating controls — if a vulnerability is mitigated by a WAF rule, network segmentation, or other defenses, its effective risk is lower.
The goal is a single score that answers the question: "If I can only patch 50 things this week, which 50 reduce my organization's risk the most?"
Step 4: Automate the Workflow
Manual prioritization doesn't scale. As your vulnerability data grows, you need automation to keep pace:
- Automated scoring — Every new vulnerability should be automatically scored against your model as soon as it's detected. No analyst should be manually looking up KEV status or EPSS scores for individual CVEs.
- Threshold-based alerting — Set clear thresholds that trigger immediate action. For example: any vulnerability with a KEV match on an internet-facing asset generates a critical alert to the remediation team.
- Integration with ticketing — Priority scores should flow directly into your remediation workflow (Jira, ServiceNow, etc.) with appropriate SLAs attached. A "Critical" priority gets a 24-hour SLA; a "Low" gets 90 days.
- Scheduled rescoring — Threat intelligence changes daily. A vulnerability that was low-priority last week might have a new public exploit today. Periodic rescoring ensures your priorities stay current.
Step 5: Measure and Iterate
A prioritization program is only as good as its outcomes. Track these metrics to validate and improve your approach:
- Mean time to remediate (MTTR) by priority tier — Are your critical findings being fixed faster than your lows? If not, your SLAs or scoring model may need adjustment.
- Exploit coverage — When a new in-the-wild exploit is disclosed, was the associated vulnerability already flagged as high priority in your system? This is the ultimate test of your model's effectiveness.
- Remediation backlog trends — Is your critical backlog growing or shrinking over time? A good prioritization program should drive the critical backlog down, even as total vulnerability counts increase.
- False positive rate — Are your teams spending time on findings that turn out to be irrelevant? High false positive rates erode trust in the system and slow down remediation.
Review these metrics monthly. Use what you learn to tune your scoring model weights, adjust thresholds, and refine your asset criticality classifications. Prioritization is not a set-it-and-forget-it activity; it's a continuous improvement loop.
Putting It All Together
Effective vulnerability prioritization isn't about patching everything. It's about patching the right things first. By combining a solid asset inventory, enriched threat intelligence, a consistent scoring model, workflow automation, and ongoing measurement, security teams can transform their vulnerability management from a reactive firefighting exercise into a proactive risk reduction program.
Automate your prioritization
Exploit Score combines ML scoring, CISA KEV, EPSS, and asset context into a single priority score that tells your team exactly where to focus.
Request a Demo