For over a decade, the Common Vulnerability Scoring System (CVSS) has been the default standard for rating the severity of security vulnerabilities. With scores ranging from 0.0 to 10.0, it provides a quick way to communicate how dangerous a flaw might be. But as the threat landscape has evolved, relying on CVSS alone has become a significant blind spot for security teams.
The Problem with CVSS-Only Prioritization
CVSS was designed to measure the intrinsic characteristics of a vulnerability: how easy it is to exploit, what access is required, and what impact a successful exploit would have. What it does not account for is whether that vulnerability is actually being exploited in the wild, or whether it matters in the context of your specific environment.
Consider this: according to research, fewer than 5% of published CVEs are ever exploited in the wild. Yet CVSS routinely rates thousands of vulnerabilities as "Critical" (9.0+) or "High" (7.0-8.9). The result? Security teams drown in alerts, patching vulnerabilities that pose little real-world risk while potentially overlooking those that attackers are actively targeting.
What's Missing: Real-World Context
Effective vulnerability prioritization requires additional context that CVSS simply doesn't provide:
- Exploit availability — Is there a known, publicly available exploit for this vulnerability? Is it being sold on underground markets?
- Active exploitation — Is this vulnerability being exploited in the wild right now? CISA's Known Exploited Vulnerabilities (KEV) catalog tracks confirmed exploitation.
- Exploit prediction — What is the statistical likelihood this vulnerability will be exploited in the near future? The Exploit Prediction Scoring System (EPSS) provides probability-based predictions.
- Asset context — Is the affected system internet-facing? Does it hold sensitive data? Is it critical to business operations?
- Industry targeting — Are threat actors specifically targeting your industry with exploits for this vulnerability?
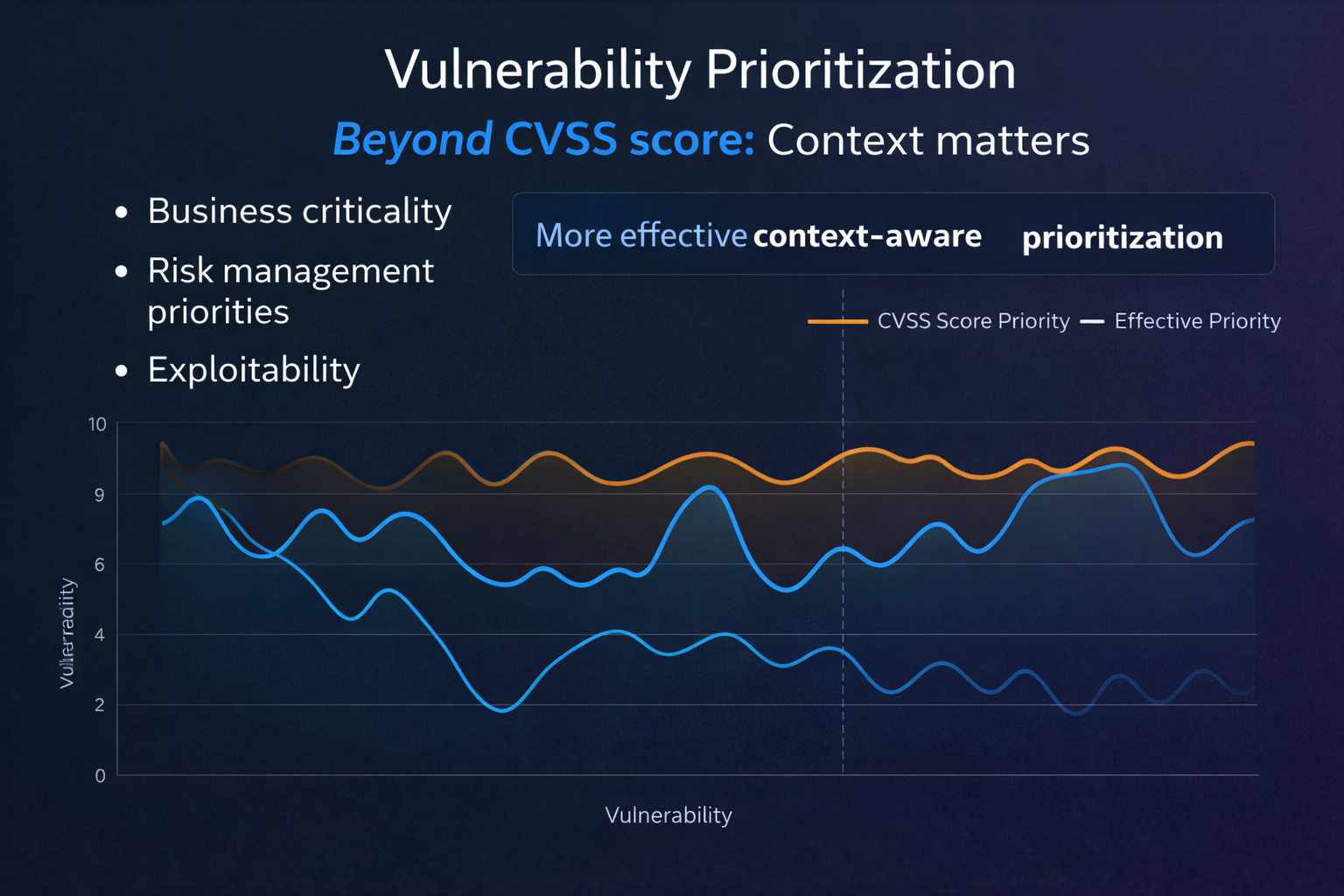
A Better Approach: Context-Aware Scoring
Modern vulnerability management platforms combine multiple intelligence sources to produce a more actionable risk score. Instead of treating every "Critical" CVSS vulnerability equally, a context-aware approach weighs factors like:
- CVSS base scores as a starting point for technical severity
- EPSS probabilities to gauge real-world exploit likelihood
- CISA KEV status to flag confirmed in-the-wild exploitation
- Threat intelligence feeds for emerging exploit activity
- Asset criticality and exposure data from your environment
- Industry-specific threat patterns and historical attack data
By combining these signals, security teams can focus their limited resources on the vulnerabilities that genuinely pose the highest risk to their organization, not just the ones with the highest CVSS number.
The Impact on Remediation Efficiency
Organizations that adopt context-aware prioritization consistently report significant improvements in their vulnerability management programs:
- Reduced remediation backlog — By focusing on what matters, teams can shrink their critical patch queue by 60-80%.
- Faster response to real threats — When a vulnerability is actively being exploited, it surfaces immediately instead of being buried in noise.
- Better alignment with business risk — Asset context ensures that a critical vulnerability on a test server isn't treated the same as one on a production database.
- Measurable risk reduction — Teams can demonstrate that they're addressing the highest-risk items first, improving overall security posture more effectively.
Getting Started
Moving beyond CVSS doesn't mean abandoning it. CVSS remains a valuable input for understanding the technical characteristics of a vulnerability. The key is to layer additional context on top of it, using exploit intelligence, asset data, and industry-specific threat models to make smarter prioritization decisions.
Machine learning has made this approach even more powerful. Modern ML models can analyze patterns across thousands of vulnerabilities, identifying which combinations of factors most strongly predict real-world exploitation, and surfacing the vulnerabilities that deserve your immediate attention.
Ready to prioritize smarter?
See how Exploit Score combines ML scoring, CISA KEV, EPSS, and asset context to surface the vulnerabilities that matter most.
Request a Demo